On 30 April 2026 a Linux vulnerability known as Copy Fail was reported. It is tracked as CVE-2026-31431 and affects the Linux kernel cryptographic subsystem in affected kernel versions.
The vulnerability can make local privilege escalation possible. This means that an attacker who can already run code as a local user in an affected environment may try to escalate privileges to root.
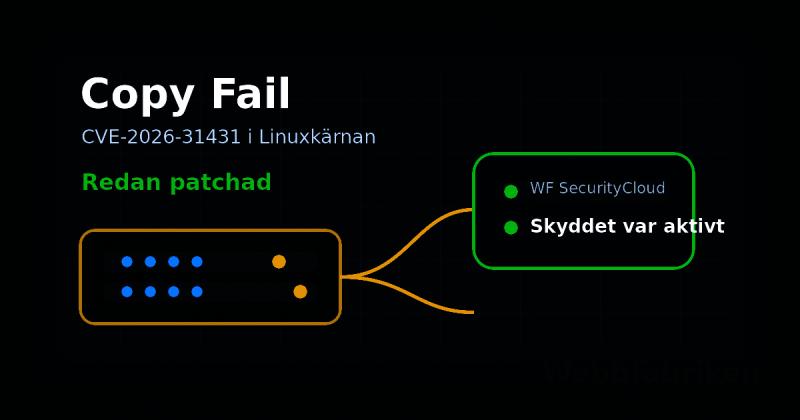
All our servers are already patched for CVE-2026-31431. In addition, WF SecurityCloud already had protection active on our own servers. For our own operations this vulnerability was therefore not a practical problem.
What Copy Fail is about
Copy Fail is based on a flaw in the Linux kernel crypto subsystem. In practice, the issue can be abused to influence page cache memory connected to readable files and create a path toward root privileges.
It is a local vulnerability. The attacker must already be able to run code on the server. It should still be taken seriously because local privilege escalation can become critical in shared environments, hosting environments and systems where multiple users or applications run on the same machine.
Systems that may be affected
Linux kernels from around 2017 onward may be affected depending on kernel version, backports and whether the vulnerable code exists in the distribution kernel.
Operating systems that may be affected depending on kernel version include Debian 10, 11 and 12, Ubuntu 18.04, 20.04, 22.04 and 24.04, AlmaLinux 8, 9 and 10, CloudLinux 7h, 8 and 9 as well as Red Hat Enterprise Linux 8 and 9.
Our status at Webbfabriken
We reviewed our servers when the information became known and verified patch levels, protection and operational status. All our servers are patched.
WF SecurityCloud also already provided active protection on our own servers. That is an important part of how we work. Patching is always necessary but an extra protection layer means that a single vulnerability does not have to become an urgent operational problem.
What customers should do
Customers in our managed environments do not need to take urgent action for CVE-2026-31431. We have handled this within our normal operational responsibility.
If you operate your own Linux servers outside our managed operations you should check kernel version, security updates and any remediation guidance from your distribution. For shared servers and hosting environments it is especially important to verify that patching has actually been completed.
Sources for technical follow up
Technical information is available from Microsoft Security, Plesk and CloudLinux.
Want us to check your own server or move hosting to an environment with active patching and WF SecurityCloud? Contact Webbfabriken and we will help you review the situation.
Need help turning this into concrete business results? Explore our Web Design, Web Development and SEO services, review Customer Cases, read our FAQ, or subscribe to our Newsletter.